Nmap is a powerful tool that is capable of generating a multitude of signatures depending on how it is used. However, if we understand the operation of the tool in general, it is easier to recognize its overall signature in network traffic. Dissecting the signature into sub-patterns one can differentiate between fingerprinting attempts that were successful and those that were not. It is important to understand that we have examined only one of the scan types that nmap can perform, the SYN half-open stealth scan. Several other scans are supported by Nmap: Tcp connect, FIN, Xmas, NULL, udp, ping, and even ftp-bounce. Expect to see these in the near future.
There’s lot of features Nmap can provide it to you : Host discovery, Port Scanning , OS detection , Auditing the security of a device by identifying the network connections, and Version detection
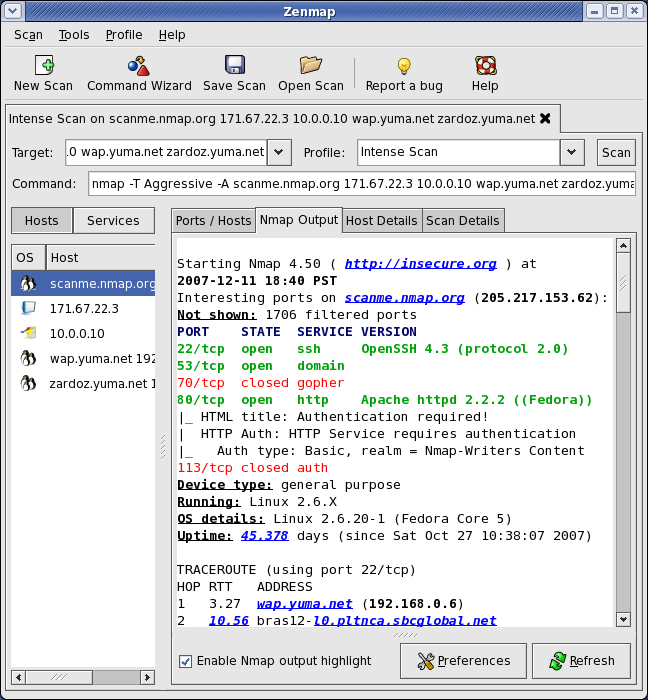
They Are two version of this Tools Command line version ( powerful one ) and GUI Version This tools available on Windows and Linux and if you decide to go with Command line you need to be experts to do that since its need lot of practice.
You can check how the GUI and Command line look like in the below pictures :
provides all the information that is needed for a well-informed, full-fledged, precisely targeted assault on a network. Such an attack would have a high probability of success, and would likely go unnoticed by organizations that lack intrusion detection capabilities.
But how can i use Nmap with Oracle, when i do some penetration testing i use this tool as command line to dicover the vulnerability, when oracle database installed on server it‘s allow to use ports in server which maybe cause vulnerability ( the simplest Way to describe ) I cannot post everything about NMAP here since i will need new book to talk about it.
the Below some examples that you could use note that I use command line version, For Example something Called Oracle Query runs a given query against the Oracle database server and returns the results
nmap -p 1521 –script oracle-query –script-args
another one could be used called Oracle hash dump which dump the database password hashes from Oracle and MS-SQL. The results are returned in format suitable and could be store in file.
For Example : CVE-2012-3137 vulnerability,. The vulnerability exists in Oracle 11g R1/R2 and allows linking the session key to a password hash. When initiating an authentication attempt as a valid user the server will respond with a session key and salt. Once received the script will disconnect the connection thereby not recording the login attempt. The session key and salt can then be used to brute force the users password, there’s patch to fix this security issue.
To avoid such an issue you should Apply Oracle security Patches, CPU patches , And OS Patches by doing maintenance like this you can minimize Vulnerability that could be happened
Thank you
Osama Mustafa