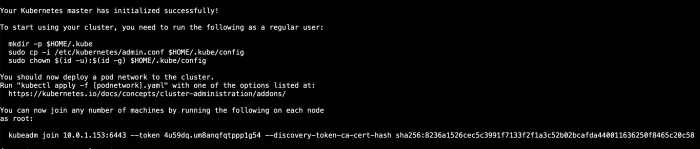
Kubernetes volumes offer a simple way to mount external storage to containers. This lab will test your knowledge of volumes as you provide storage to some containers according to a provided specification. This will allow you to practice what you know about using Kubernetes volumes.
Create a Pod That Outputs Data to the Host Using a Volume
- Create a Pod that will interact with the host file system by using vi maintenance-pod.yml.
apiVersion: v1
kind: Pod
metadata:
name: maintenance-pod
spec:
containers:
- name: busybox
image: busybox
command: ['sh', '-c', 'while true; do echo Success! >> /output/output.txt; sleep 5; done']
- Under the basic YAML, begin creating volumes, which should be level with the containers spec:
volumes:
- name: output-vol
hostPath:
path: /var/data
- In the containers spec of the basic YAML, add a line for volume mounts:
volumeMounts:
- name: output-vol
mountPath: /output
The complete YAML will be
apiVersion: v1
kind: Pod
metadata:
name: maintenance-pod
spec:
containers:
- name: busybox
image: busybox
command: ['sh', '-c', 'while true; do echo Success! >> /output/output.txt; sleep 5; done']
volumeMounts:
- name: output-vol
mountPath: /output
volumes:
- name: output-vol
hostPath:
path: /var/data
Create a Multi-Container Pod That Shares Data Between Containers Using a Volume
- Create another YAML file for a shared-data multi-container Pod by using vi shared-data-pod.yml
- Start with the basic Pod definition and add multiple containers, where the first container will write the output.txt file and the second container will read the output.txt file:
apiVersion: v1
kind: Pod
metadata:
name: shared-data-pod
spec:
containers:
- name: busybox1
image: busybox
command: ['sh', '-c', 'while true; do echo Success! >> /output/output.txt; sleep 5; done']
- name: busybox2
image: busybox
command: ['sh', '-c', 'while true; do cat /input/output.txt; sleep 5; done']
Set up the volumes, again at the same level as containers with an emptyDir volume that only exists to share data between two containers in a simple way:
volumes:
- name: shared-vol
emptyDir: {}
Mount that volume between the two containers by adding the following lines under command for the busybox1 container:
volumeMounts:
- name: shared-vol
mountPath: /output
For the busybox2 container, add the following lines to mount the same volume under command to complete creating the shared file:
volumeMounts:
- name: shared-vol
mountPath: /input
The complete file
Finish creating the multi-container Pod using kubectl create -f shared-data-pod.yml.
apiVersion: v1
kind: Pod
metadata:
name: shared-data-pod
spec:
containers:
- name: busybox1
image: busybox
command: ['sh', '-c', 'while true; do echo Success! >> /output/output.txt; sleep 5; done']
volumeMounts:
- name: shared-vol
mountPath: /output
- name: busybox2
image: busybox
command: ['sh', '-c', 'while true; do cat /input/output.txt; sleep 5; done']
volumeMounts:
- name: shared-vol
mountPath: /input
volumes:
- name: shared-vol
emptyDir: {}
And you can now apply the YAML file.
Cheers
Osama