I tried to make this article as simple as it’s, since i faced different issue during this and couldn’t find any articles or Oracle Support document that related to any of the issue i faced so i am writing this blog to share it and could be useful for people.
Weblogic Server comes with an Embedded LDAP Server which acts as the Default Provider for authentication, authorization and role mapping .Since authentication is based on JAAS ( Java Authentication and Authorization Service), we can have external providers as well one of these external provider is Active directory authentication.
Important note :- Before start any of these steps you should ask your system administrator to create active directory user the purpose of this use only to read active directory information and system administrator should provide you with distinguished name (DN) for this user, and Assign it to Administrator Group. This is required as Active Directory gives connection only to Admin User.
Steps:
- to enable the port you have to do different things before start doing the configuration from weblogic side, since we are using SSL Port and not the unsecured one you have to import the certificate first, the certificate could be provided to you by the system administrator, in my case to avoid any wasting of time i used Jdeveloper to import the certificate because the Jdeveloper having the capability to connect to the LDAP server in both way (636 or 389 ) once you are connected you can import the certificate.
- Now after importing the certificate go the weblogic server and run the below command i choose to save my certificate under #WLS_HOME/wlserver/server/lib :
keytool -import -trustcacerts -alias NEWAD -file Certifcate_name -keystore NEWAD.jks -storepass Oracle123
- Alias : the alternative name for the certificate you can choose yours but make it clear.
- file : the certificate location where you imported from Jdeveloper or by system admin.
- keystore : the output file and should be JKS format.
- storepass : the password for the imported certificate.
- once you are done from the above steps, shutdown the adminserver and managed server using the console of the weblogic and edit the setDomainEnv.sh or setDomainEnv.cmd depend on your operating system then add the below lines ( the location of the JKS file)
JAVA_OPTIONS=”${JAVA_OPTIONS} -Djavax.net.ssl.trustStore=/u01/Oracle/Middleware/fmw_soa/wlserver/server/lib/NEWAD.jks
- Now start the AdminServer, the following steps should be done before testing anything.
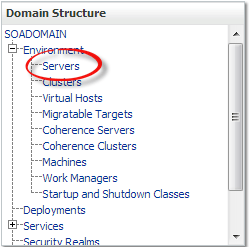
- as you see from the below picture choose custom keystore and start fill the information which is the location for the JKS without putting the file, the password for the certificate that you choose it while importing.
- After that you should modify the SSL part, this time you have to remember the alias and the password like the below :-
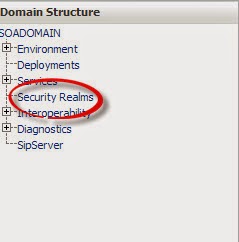
- Under Security Realms on the left panel choose providers > New providers
- Weblogic having different external provider > but we want Active Directory, make sure to choose the right one.
- Some changes should be done after the provider created which is the order and flag of the provider , for the order the Active directory provider should come first and flag should be SUFFICIENT.
- Start fill the information like the below which AD Host, Active directory user ( Should be created first ), Password for the user, User Base DN and in the last Group Base DN ” Don’t change anything else” and check on SSL enabled.
- For testing and if the provider working or not, under user and groups you should be able to see the AD users and groups now in the weblogic.
- Error [Security:090834]No LDAP connection could be established. ldaps://HOST:636 Cannot connect to the LDAP server
- weblogic.security.providers.authentication.LDAPAtnDelegateException: [Security:090294]could not get connection
- Caused by: java.lang.reflect.InvocationTargetException
- Caused by: netscape.ldap.LDAPException: General SSLEngine problem (91); Cannot connect to the LDAP server
- Caused by: javax.net.ssl.SSLHandshakeException: General SSLEngine problem
- Caused by: sun.security.validator.ValidatorException: PKIX path building failed
- Caused by: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target